Turn TPRM Data Challenges into Opportunities
Managing an effective Third-Party Risk Management (TPRM) program is a significant challenge for any organization. As your network of third-party vendors expands, so do the complexities of assessing and mitigating their risks. Common challenges include:
- Growing volumes of third parties to assess and monitor
- Limited internal resources to handle increasing reviews
- Difficulty maintaining visibility into evolving risks
- Inconsistent or incomplete data from third parties
- Conflicting internal (vendor self-attested) signals with external (ratings providers, perimeter scanning)
Instead of being bogged down by manual assessments and fragmented data, empower your team with proprietary controls-based intelligence from ProcessUnity’s Global Risk Exchange.
The ProcessUnity Global Risk Exchange:
Real Risk Data Intelligence to Extend Your Team
The ProcessUnity Global Risk Exchange is the world’s largest dataset of controls intelligence contextualized by expert associations to firmographic and technographic data, external threat intelligence, Common Weakness Enumerations (CWEs), and MITRE ATT&CK killchains. Our customers leverage this data to experience a:
*Read the ProcessUnity Global Risk Exchange Value Perspective from GRC 20/20 for more details on how we maximize customer return on investment.
Global Risk Exchange Highlights
The Global Risk Exchange is powered by the most comprehensive and sophisticated cybersecurity controls dataset in the world, combining control attestations from over 18,000 companies and vendor profiles on over 370,000 companies, firmographic data, comparative analysis on similar companies to benchmark control implementation and effectiveness, and expert associations to Common Weakness Enumerations (CWEs), MITRE ATT&CK Techniques, and technographic data.
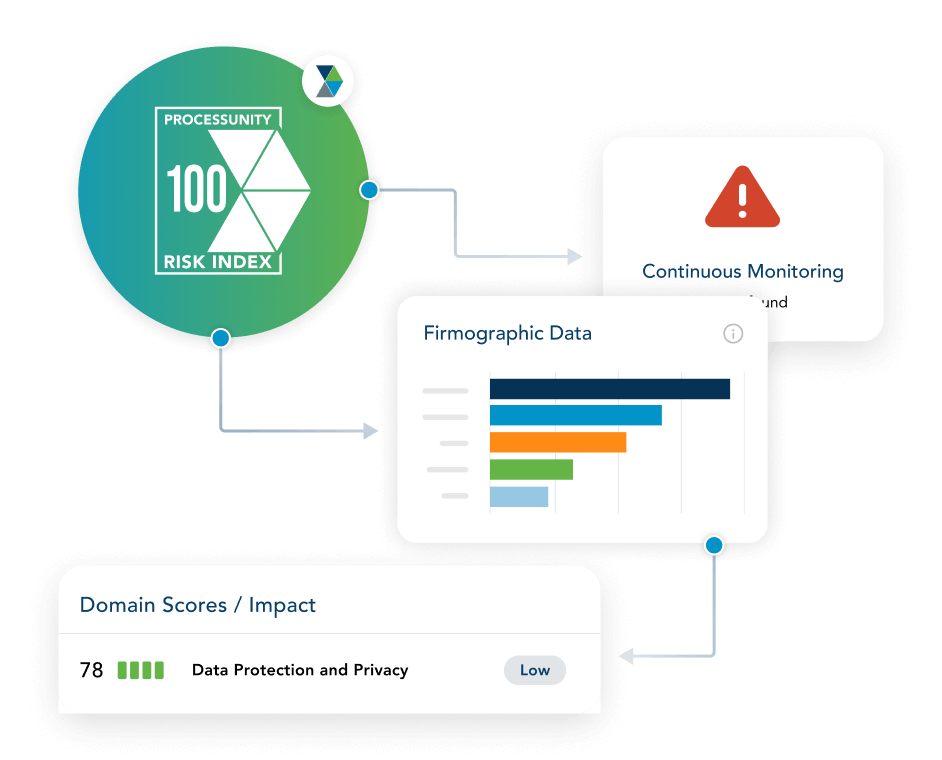
Powered by the Exchange’s controls-based intelligence, ProcessUnity Risk Index is an actionable risk rating that combines internally informed control data with externally observed risk signals.
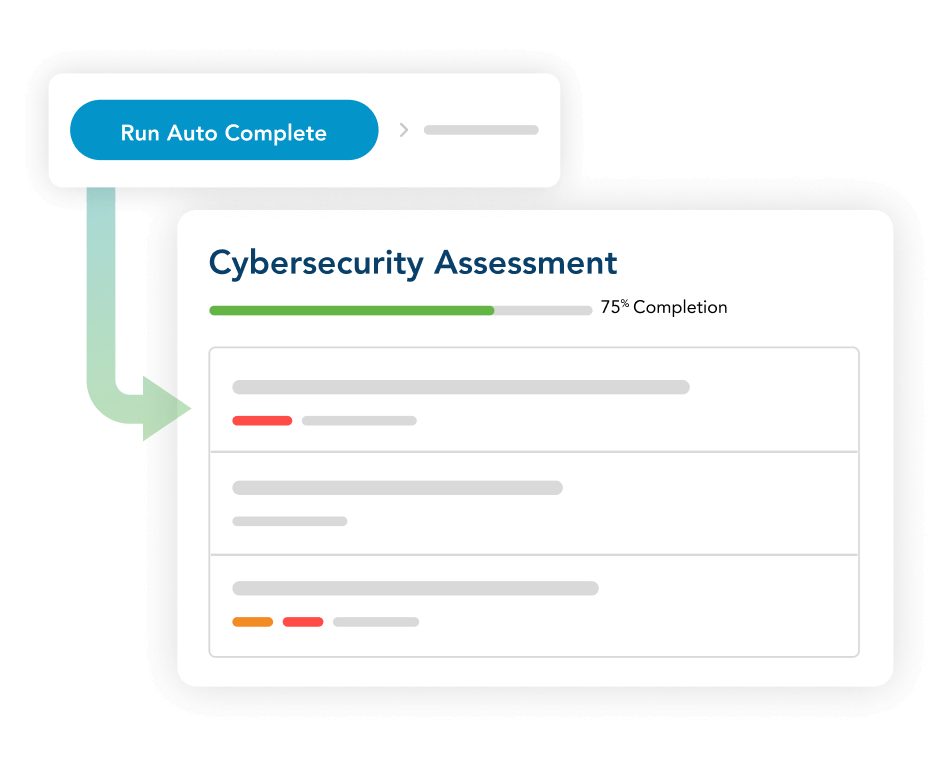
AI-powered Assessment Autofill pre-populates a vendor’s cybersecurity assessment and control attestations by analyzing submitted documentation (SOC 2 reports, ISO certifications, internal policies and procedures, and other control evidence documents).
Global Risk Exchange data is deeply embedded into the TPRM lifecycle at key decision points during onboarding, due diligence, and continuous monitoring.
See How the Global Risk Exchange Accelerates Vendor Assessments
Request a DemoRelevant TPRM Data and Powerful Insights to Extend Your Team
Improve Third-Party Engagement
The Global Risk Exchange is built on participation from over 18,000 vendors, including large, hard-to-assess third parties that typically don’t respond to assessment and information requests. Via the Exchange, third-party vendors actively participate in their ProcessUnity Risk Index score, ensuring that their Risk Index profile is representative of their true risk posture.
Third parties in the Global Risk Exchange include:
- 80% of Fortune 1000 companies
- 4 of the top 5 cloud providers
- 12 of the top 20 law firms
- 4 of the top 5 private equity firms
- The top 4 accounting firms

Power Data Action
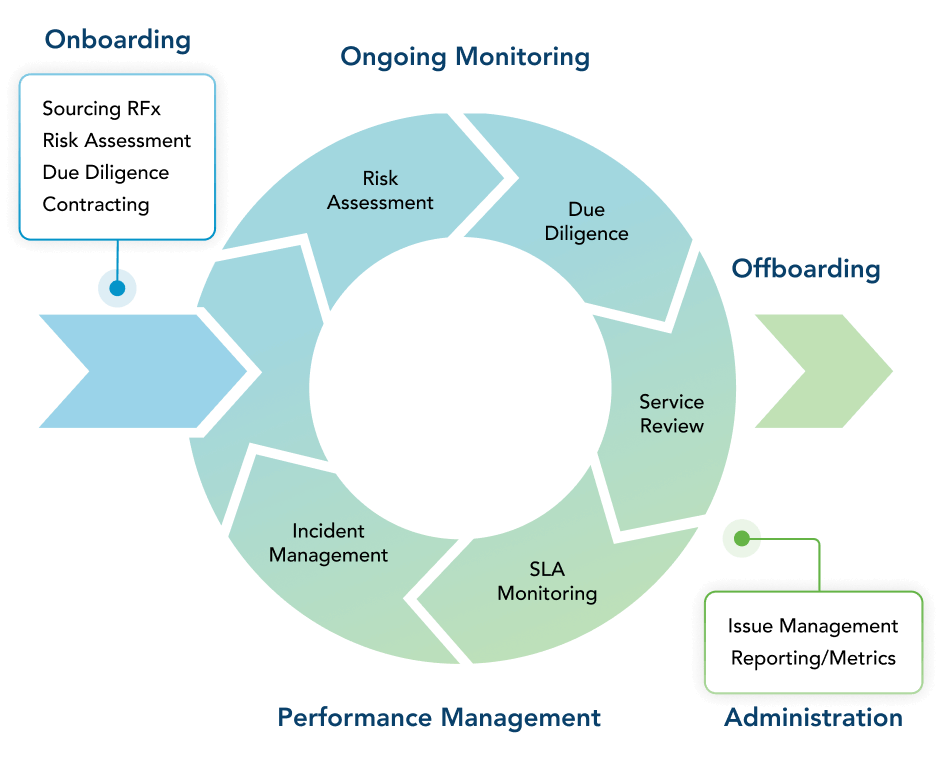
Combine the power of workflow and data at every stage in the third-party lifecycle. Global Risk Exchange data via ProcessUnity Risk Index scores and control-level detail are deeply embedded into ProcessUnity’s TPRM platform during:
Onboarding: Pre-populate vendor intake with firmographic information and prioritize vendors for initial pre-contract due diligence with Risk Index scores.
Due Diligence: Perform an early internal review of controls, dynamic scoping, and assessment prep-population. Leverage ProcessUnity’s AI-driven Evidence Evaluator to review and validate vendor control evidence.
Continuous Monitoring: Get filtered, relevant notifications about meaningful changes in risk posture such as score changes and breach notifications, then leverage workflow steps to take immediate remedial action.

Calculate Your Potential Savings with ProcessUnity
Build a business case to uplevel your Third-Party Risk Management program. Answer a few short questions and generate your custom savings report.
Calculate Your ROI Now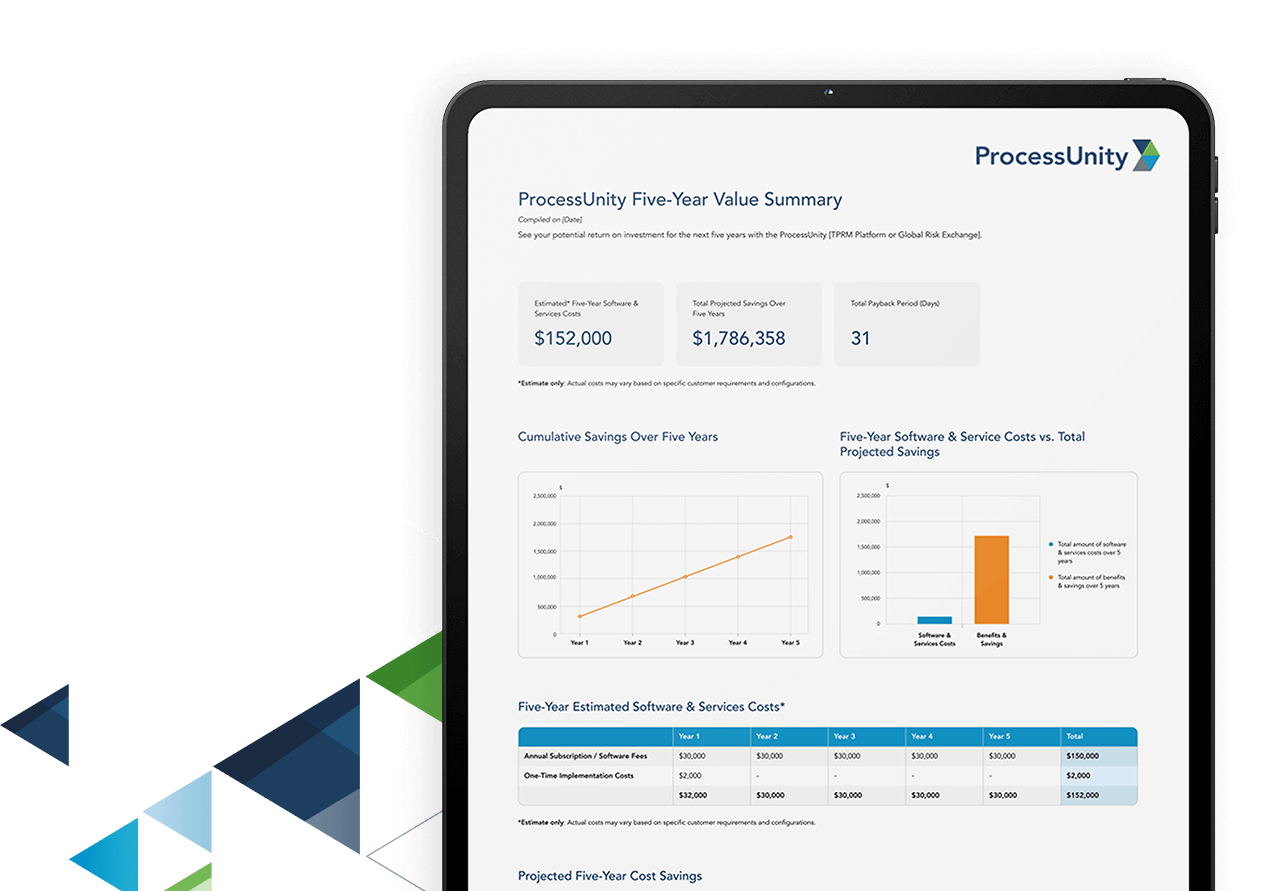
Frequently Asked Questions
A third-party risk assessment is the process of evaluating a third party’s potential risk to the business across areas such as cybersecurity, regulatory compliance, and operational practices to ensure they align with your organization’s standards.
The five phases of third-party risk management are:
- Planning and Scoping – Identify critical third parties and define risk management goals.
- Due Diligence and Selection – Assess third-party risk before onboarding.
- Contract Negotiation – Set clear expectations for compliance, security, and performance.
- Ongoing Monitoring – Continuously assess third-party risk and performance.
- Termination and Transition – Manage offboarding with plans for continuity and compliance.
A third-party risk assessment exchange contains validated risk assessments, completed questionnaires, vendor risk profiles, and supporting documentation. It provides fast, reliable access to third-party risk data, even for hard-to-reach third parties, and accelerates risk decision-making.
Monitoring third-party risk involves continuous assessments, integration of external risk data, real-time alerts, and regular third-party performance reviews to identify and address emerging threats proactively.
Here’s how to perform a third-party risk assessment:
- Define the scope and objectives of your assessment based on the third party’s inherent risk levels.
- Gather third-party information through tailored questionnaires.
- Leverage a third-party risk assessment library to systematically evaluate and verify specific risk areas.
- Analyze assessment results to identify potential vulnerabilities.
- Develop targeted remediation plans to address identified risks.
- Document the process for future reference and compliance purposes.
Next Steps:
Schedule a ProcessUnity Platform Demo
Our team is here to show you how forward-thinking organizations are elevating their
Third-Party Risk Management programs and practices to maximize risk reduction. Start
your journey with ProcessUnity today.