New Guide Offers Expert Advice for Effective and Efficient Vendor-Risk Processes
A robust, effective, and efficient Third-Party Risk Management (TPRM) program is essential to protect organizations – to mitigate the risk companies face from third-parties and to ensure they are in TPRM compliance with regulators.
We have found that those who define and develop strong TPRM programs that are thoughtfully planned, rooted in best practices, and designed to incrementally improve lead to healthier, safer companies that are better prepared to face both expected and unexpected challenges.
Your goals ultimately determine the extent of your Third-Party Risk Management investment. But no matter where you are, there is always an opportunity for growth: whether you are an informal program thrown together out of necessity, a reactive program that is a bit more mature, a proactive program that incorporates sound structure and many best practices, or an optimized program that functions at a high level – there are opportunities to advance and strengthen your organization’s TPRM program.
ProcessUnity is Sharing the Third-Party Risk Management Lessons We Learned
In our expert guide, Third-Party Risk Management Best Practices, our team details lessons learned from hundreds of real-world efforts working with organizations to improve their vendor-risk programs. We outline a set of clear recommendations to follow to enhance your company’s program, no matter what stage it is at.
Conceptually, Third-Party Risk Management is simple to understand – put a spotlight on the policies and procedures, risks and controls of third parties and ensure those vendors are doing things how they should. The execution, however, is more challenging.
Our guide takes readers through the process of building an effective and efficient TPRM program. Written by a team of hands-on strategy and automation experts, it defines the stages of third-party risk management programs, explores key elements essential at each stage, and makes specific recommendations on how to incorporate improvements.
Specifically, Third-Party Risk Management Best Practices:
- Defines the building blocks of third-party risk management programs
- Explores the processes for vendor onboarding and monitoring
- Examines the importance of inherent risk and how it should be incorporated into programs
- Discusses residual risk and how to determine ongoing review cadences for vendors
- Recommends ways to integrate content and service offerings into programs
- Provides direction on how to perform self-assessments of your organization’s third-party risk management program
- Suggests actions to improve your program
Download Third-Party Risk Management Best Practices now and learn how to chart your company’s path to a more effective and efficient TPRM program.
Related Articles

Cut Risk, Not Corners: Streamlining the...
The modern organization relies on a larger, more integrated network of third parties and suppliers..
Learn More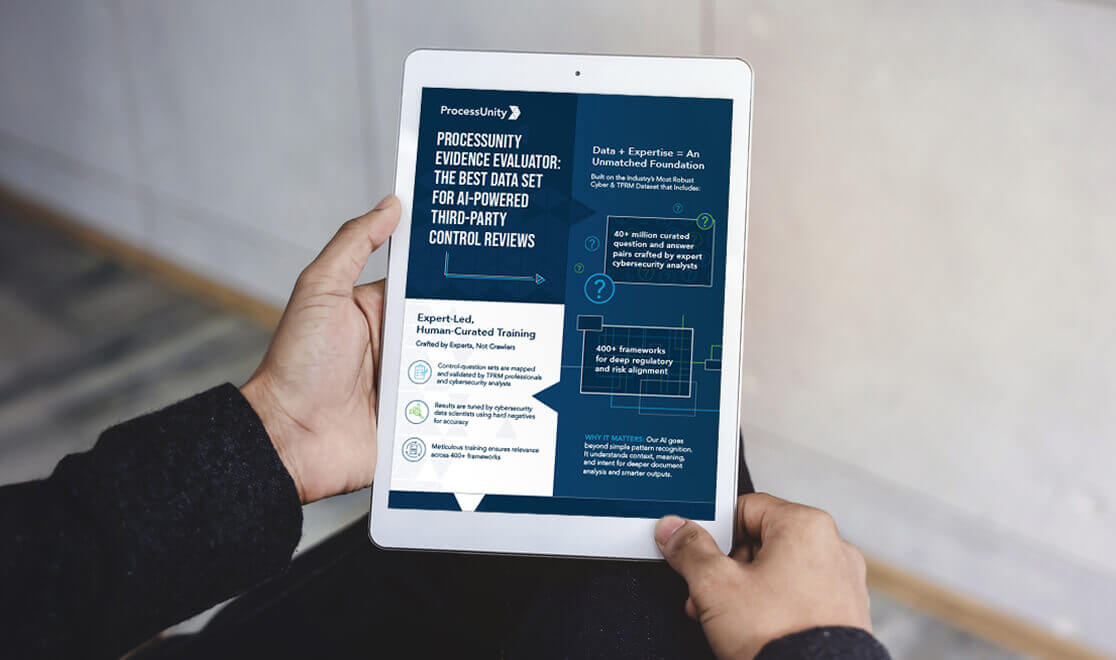
Accelerate Control Reviews with ProcessUnity’s Evidence...
Third-party risk assessments are becoming increasingly complex and resource-intensive. Manual evidence reviews create bottlenecks, inconsistent..
Learn More
5 Cybersecurity Frameworks Financial Institutions Can’t...
Regulatory pressure is intensifying — and financial institutions are feeling the heat. In 2024, the..
Learn More
ProcessUnity Evidence Evaluator: AI-Based Third-Party Controls...
See how ProcessUnity’s GenAI-powered feature simplifies third-party risk assessments. In just 60 seconds, discover how..
Learn More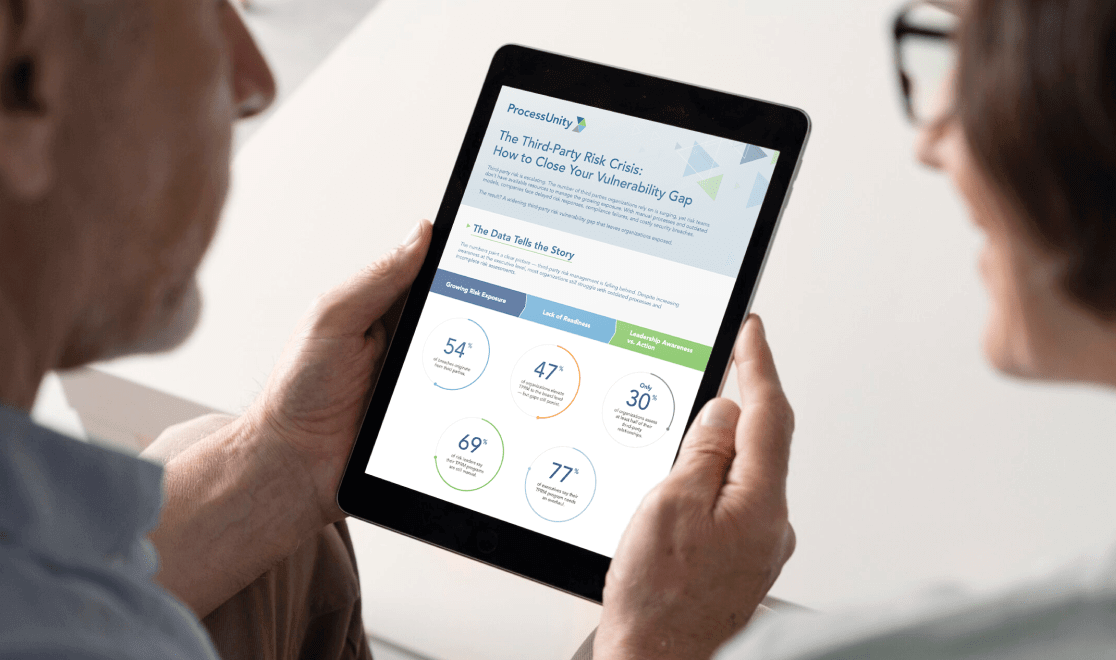
How to Close Your Third-Party Risk...
Is your organization exposed to hidden third-party risks that could create dangerous blind spots in..
Learn More
8 Ways Your Business Benefits from...
Cyber threats are intensifying. Regulatory scrutiny is increasing. Legacy assessments simply can’t keep pace. To..
Learn More
5 Critical Regulations Reshaping TPRM in...
The pressure on financial institutions to manage third-party risk is mounting — and the stakes..
Learn More
How Third-Party Vendor Risk Disrupts Business...
Your third-party vendors are delivering on time, business operations are efficient and planned, and customers..
Learn More
10 Critical Third-Party Risk Management Challenges...
Every vendor relationship can introduce potential vulnerabilities to your business, and in today's hyperconnected business..
Learn More
Ensure Ongoing DORA Compliance Across Your...
The Digital Operational Resilience Act (DORA) is a regulatory framework established by the European Union..
Learn More
5 Essential Steps to Modernize Your...
Third-party relationships have become a critical vulnerability point - with 54% of security breaches occurring..
Learn More
Third-party risk: Re-thinking vendor assessments
Third parties can introduce substantial risk into global supply networks, but rigorous vendor risk assessments..
Learn More
ProcessUnity Introduces a Revolutionary Platform to...
Threat and Vulnerability Response Platform Utilizes Proprietary Threat Intelligence to Rapidly Identify Third-party Gaps and..
Learn More
Revolutionizing Response to Emerging Third-Party Cybersecurity...
Introducing ProcessUnity’s New Threat and Vulnerability Response Platform to Quickly Identify Emerging Threats and Assess..
Learn More
How Organizations and Vendors Use a...
A third-party risk exchange is a transformative concept designed to make third-party risk management (TPRM)..
Learn More
ProcessUnity Introduces Industry’s All-In-One Third-Party Risk...
Completes Integration with Global Risk Exchange; Augments Resources to Extend Coverage to More Outsourced Service..
Learn More
Mature Your Cyber Program with a...
Risk-based cybersecurity risk management is the process of identifying, tracking and mitigating the risks to..
Learn More
Controls-Based Versus Risk-Based Cybersecurity Programs
In the face of an escalating regulatory burden and increasingly common data breaches, many teams..
Learn More
Manage Cybersecurity Risk with the SCF...
The Secure Controls Framework (SCF) Risk Management Model can be a powerful tool for teams..
Learn More
Optimize Vendor Onboarding by Aligning with...
During the vendor onboarding process, both cybersecurity and procurement manage the amount of risk brought..
Learn More
3 Takeaways about Anti-Bribery and Corruption...
Anti-bribery and corruption programs grant businesses visibility into their internal practices and third-party networks to..
Learn More
Properly Scoping Vendor Due Diligence Drives...
Properly Scoping Vendor Due Diligence Saves Both Time and Money One of the costliest mistakes..
Learn More
Security Assessments 2.0: The Next Generation...
The more things change, the more they stay the same. It's a well-worn adage that..
Learn More
How to Conduct Third-Party Due Diligence
Identifying and engaging with the right partners is essential to the success of most businesses...
Learn More
Evaluating Security Risk When Onboarding New...
In today’s tightly interwoven supply chains and highly competitive markets, organizations must continuously evaluate and..
Learn More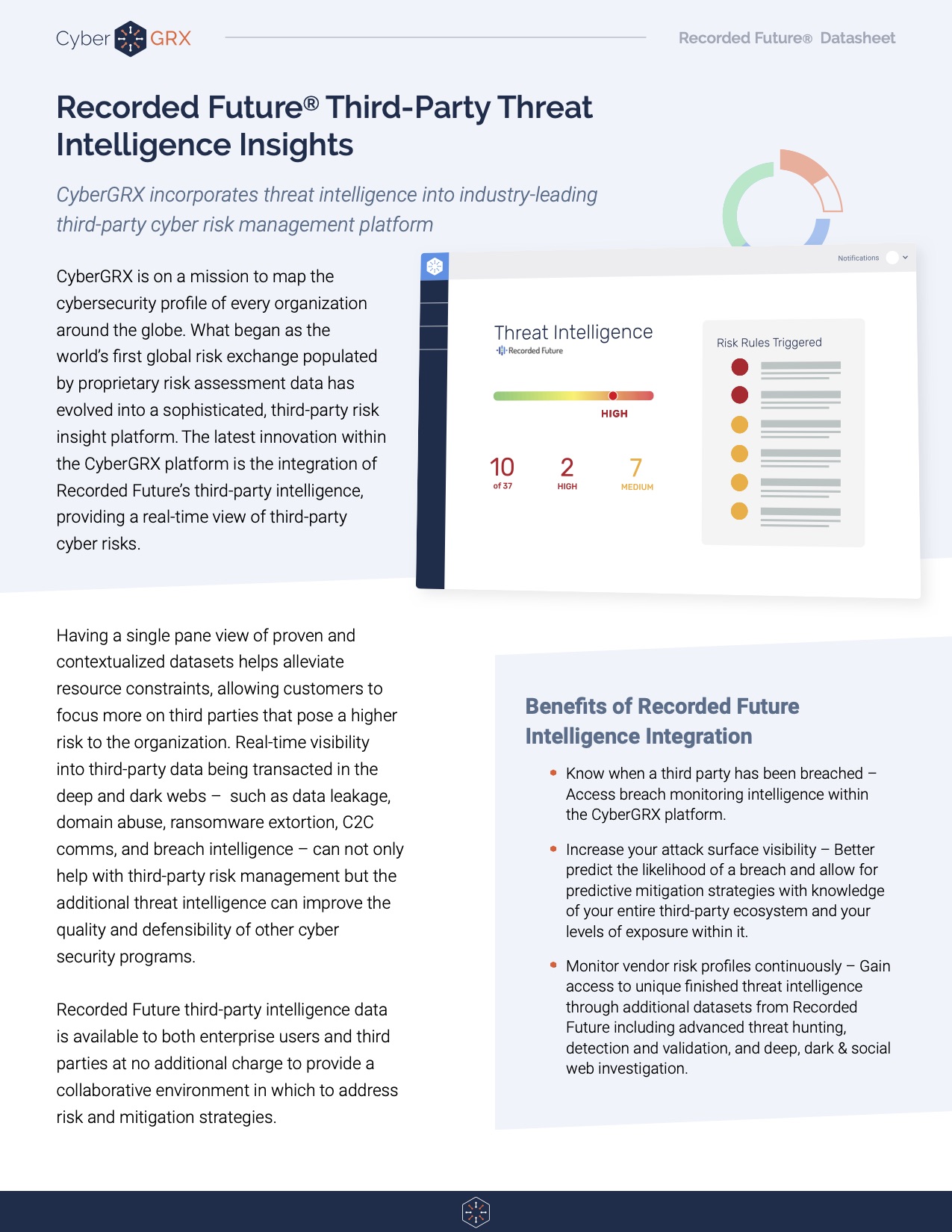
Recorded Future Third-Party Threat Intelligence Insights
Having a single pane view of proven and contextualized datasets helps alleviate resource constraints, allowing..
Learn More
5 Areas to Mitigate Risk in...
If you work within a Vendor Risk Management (VRM) team, you know that third-party risk..
Learn More
5 Tips to Improve Your Vendor...
Vendor due diligence is essential to any third-party risk management program. However, no two due diligence processes are..
Learn More
Inherent Risk vs. Residual Risk in...
Conducting a thorough vendor risk analysis is an integral step in Vendor Risk Management. However,..
Learn More
What is Third-Party Risk Management?
Third-Party Risk Management is the process of identifying, managing and mitigating risks present in a vendor relationship. This..
Learn More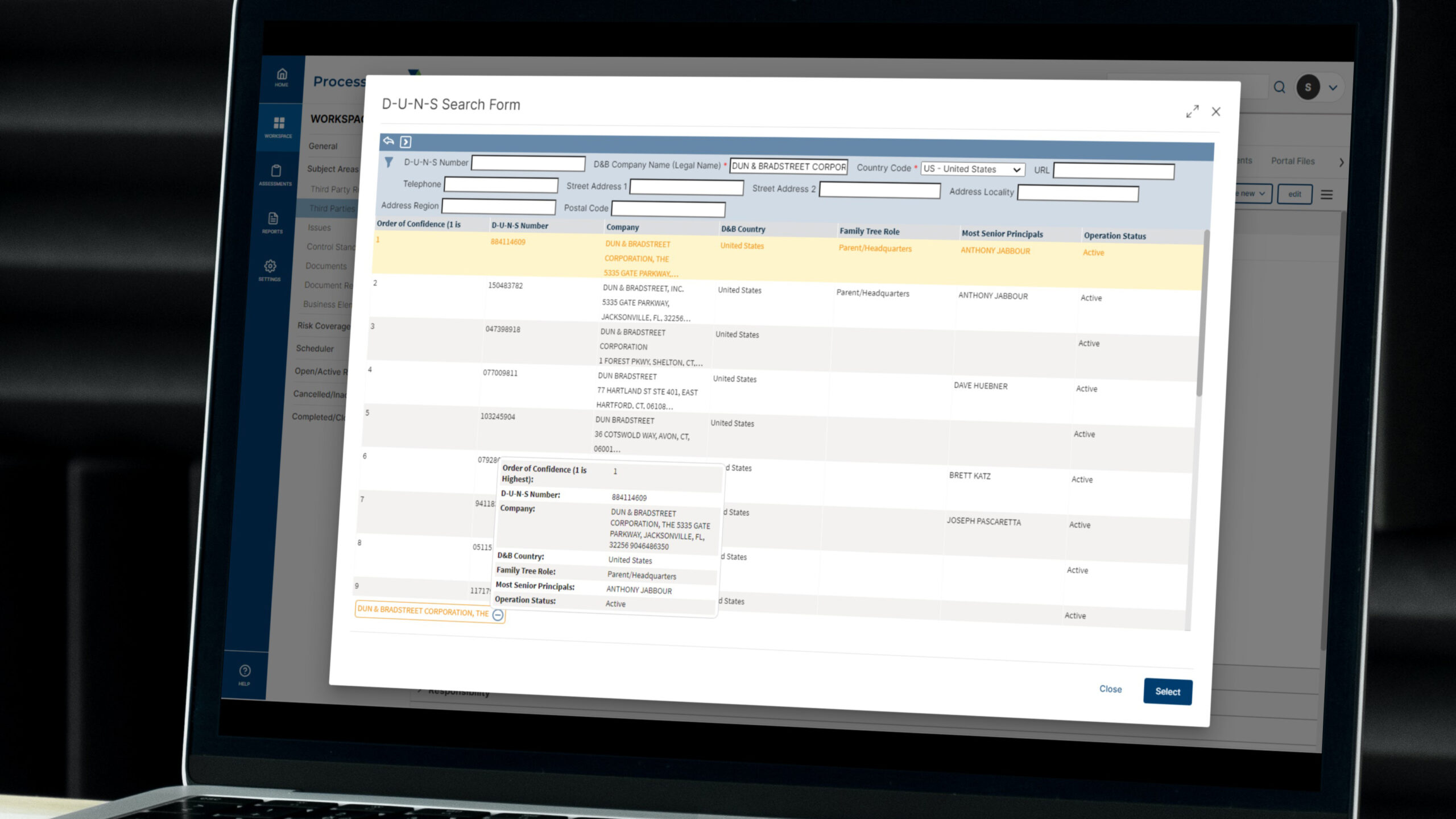
ProcessUnity Vendor Identity Intelligence with Dun...
ProcessUnity Vendor Identity Intelligence seamlessly and automatically incorporates D&B’s D-U-N-S Search and Beneficial Owner Search..
Learn More
Anti-Bribery & Corruption (ABAC) in Business...
The impacts of corruption can be very severe and have been historically well documented. On a political level, corruption – however and wherever..
Learn More
What Is Third-Party Risk Management: The...
The recent SolarWinds breach has reminded news organizations, businesses, and leadership teams around the world..
Learn More
8 Benefits of Completing a CyberGRX...
CyberGRX modernizes and streamlines redundant and inefficient processes that come with shared and static..
Learn More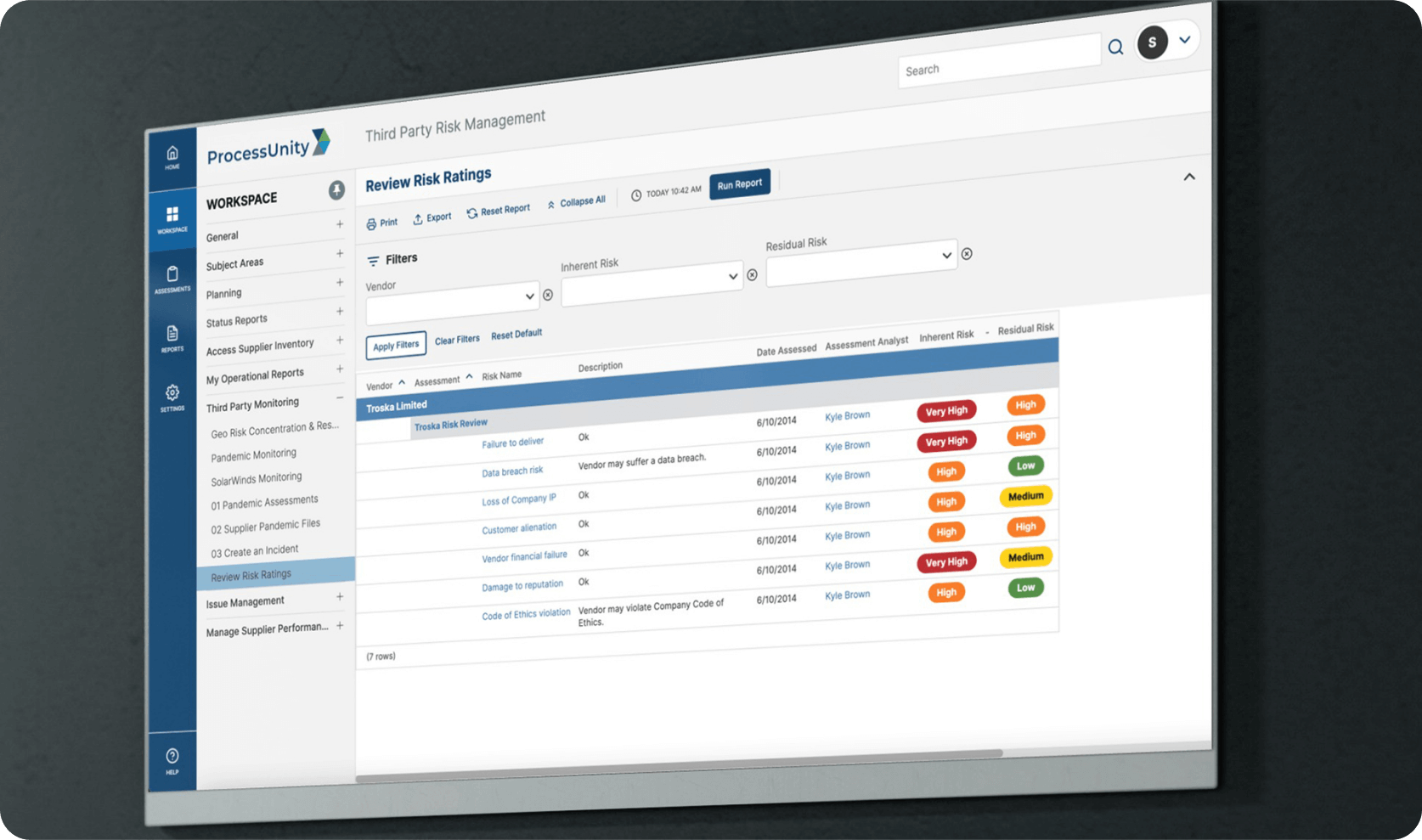
Best Practice Program for ProcessUnity Vendor...
ProcessUnity Vendor Risk Management (VRM) protects companies and their brands by reducing risks from third-party vendors and..
Learn More
ProcessUnity Vendor Financial Intelligence Powered By...
ProcessUnity Vendor Financial Intelligence (VFI) with RapidRatings seamlessly incorporates RapidRatings’ financial health ratings into ProcessUnity’s Third-Party..
Learn More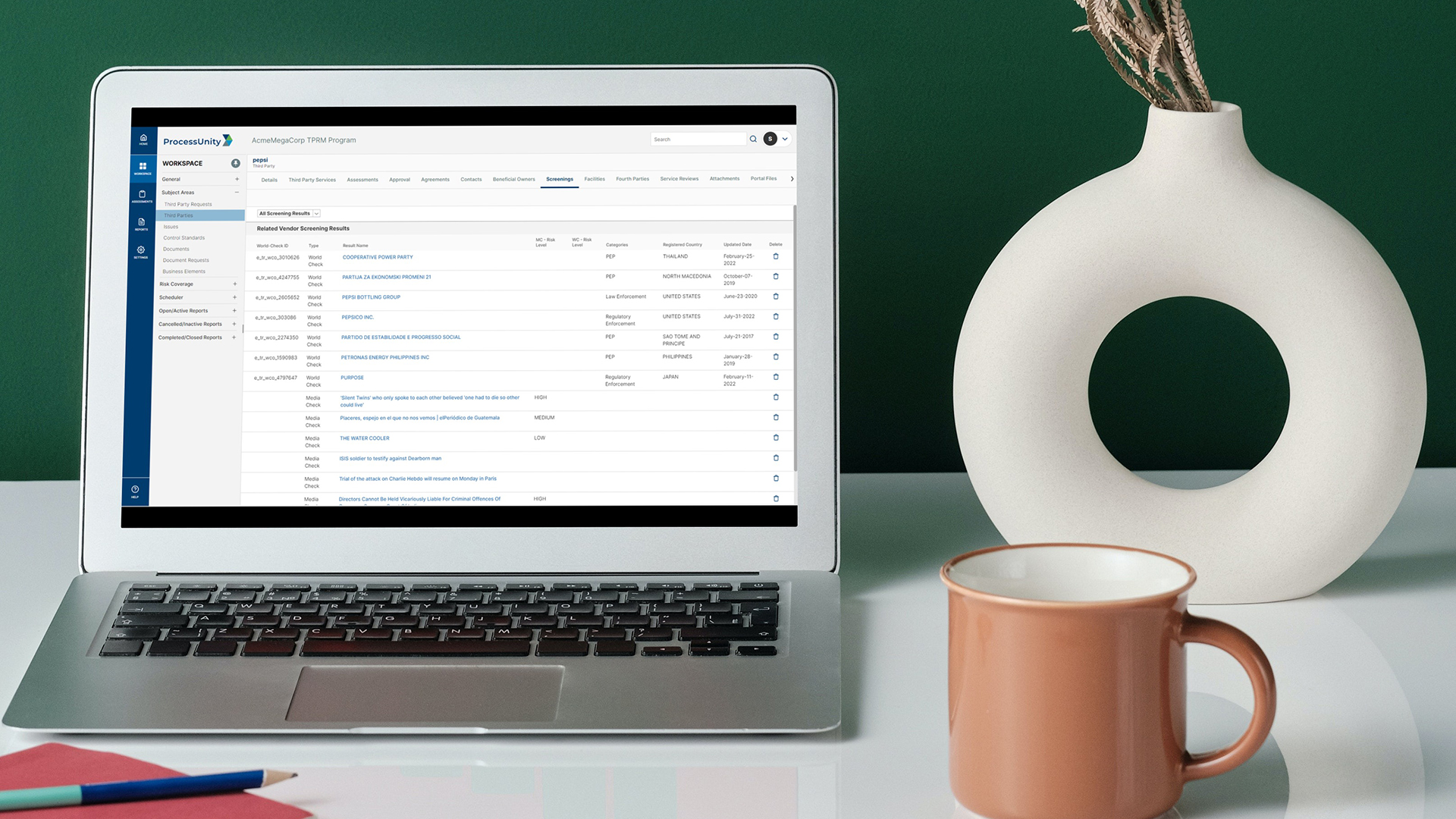
Vendor Screening Intelligence with Refinitiv
ProcessUnity Vendor Screening Intelligence (VSI) embeds LSEG World-Check One’s third-party screening capabilities into ProcessUnity’s Third-Party Risk..
Learn More
How to Stay Ahead of Risk...
Managing risk through pre-contract vendor due diligence in a digitally connected world Thanks to increasing..
Learn MoreAbout Us
ProcessUnity is a leading provider of cloud-based applications for risk and compliance management. The company’s software as a service (SaaS) platform gives organizations the control to assess, measure, and mitigate risk and to ensure the optimal performance of key business processes. ProcessUnity’s flagship solution, ProcessUnity Vendor Risk Management, protects companies and their brands by reducing risks from third-party vendors and suppliers. ProcessUnity helps customers effectively and efficiently assess and monitor both new and existing vendors – from initial due diligence and onboarding through termination. Headquartered outside of Boston, Massachusetts, ProcessUnity is used by the world’s leading financial service firms and commercial enterprises. For more information, visit www.processunity.com.