Content & Integrations
ProcessUnity BitSight Connector
Incorporate BitSight Cybersecurity Ratings into Your Vendor Risk Management Program
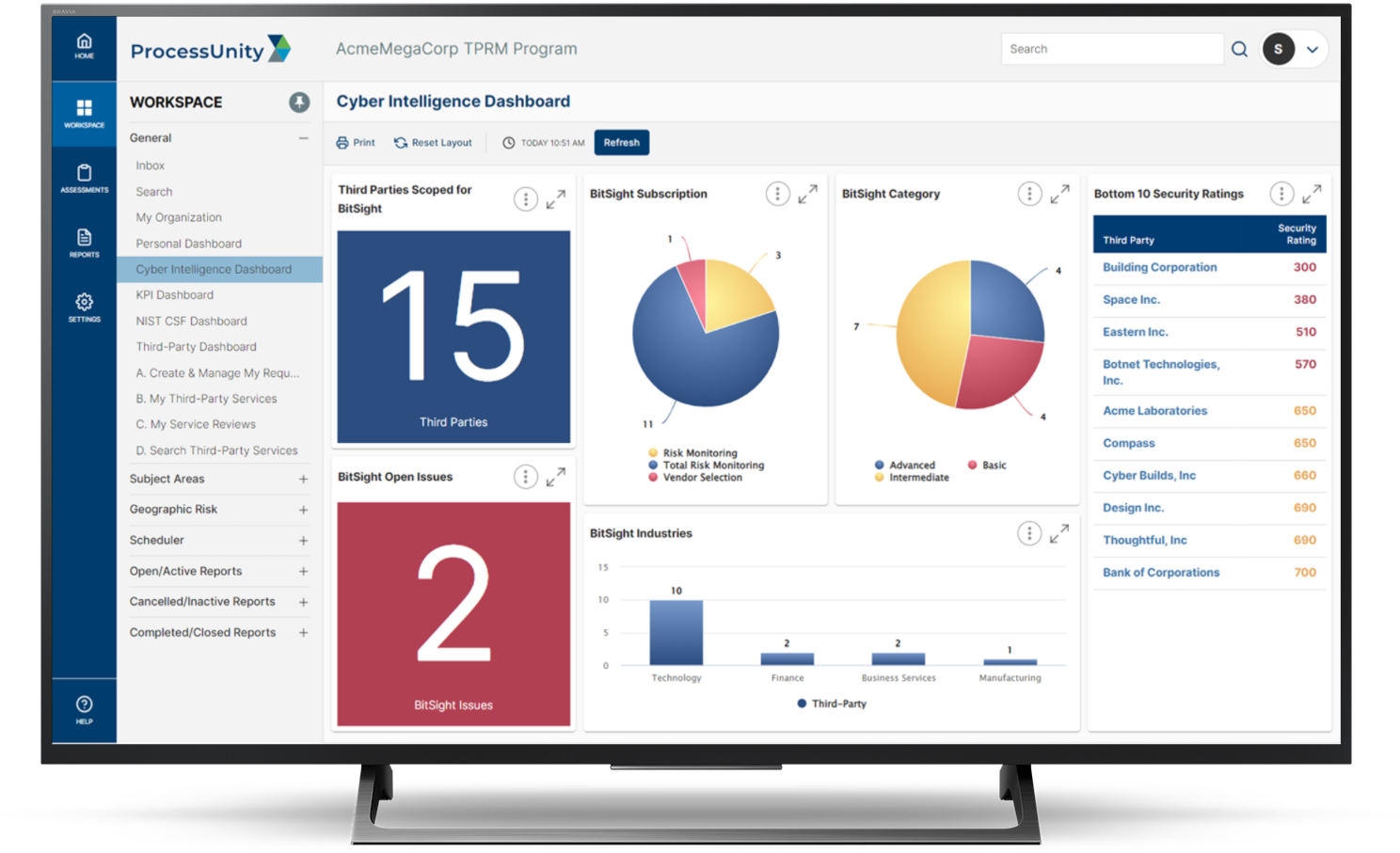
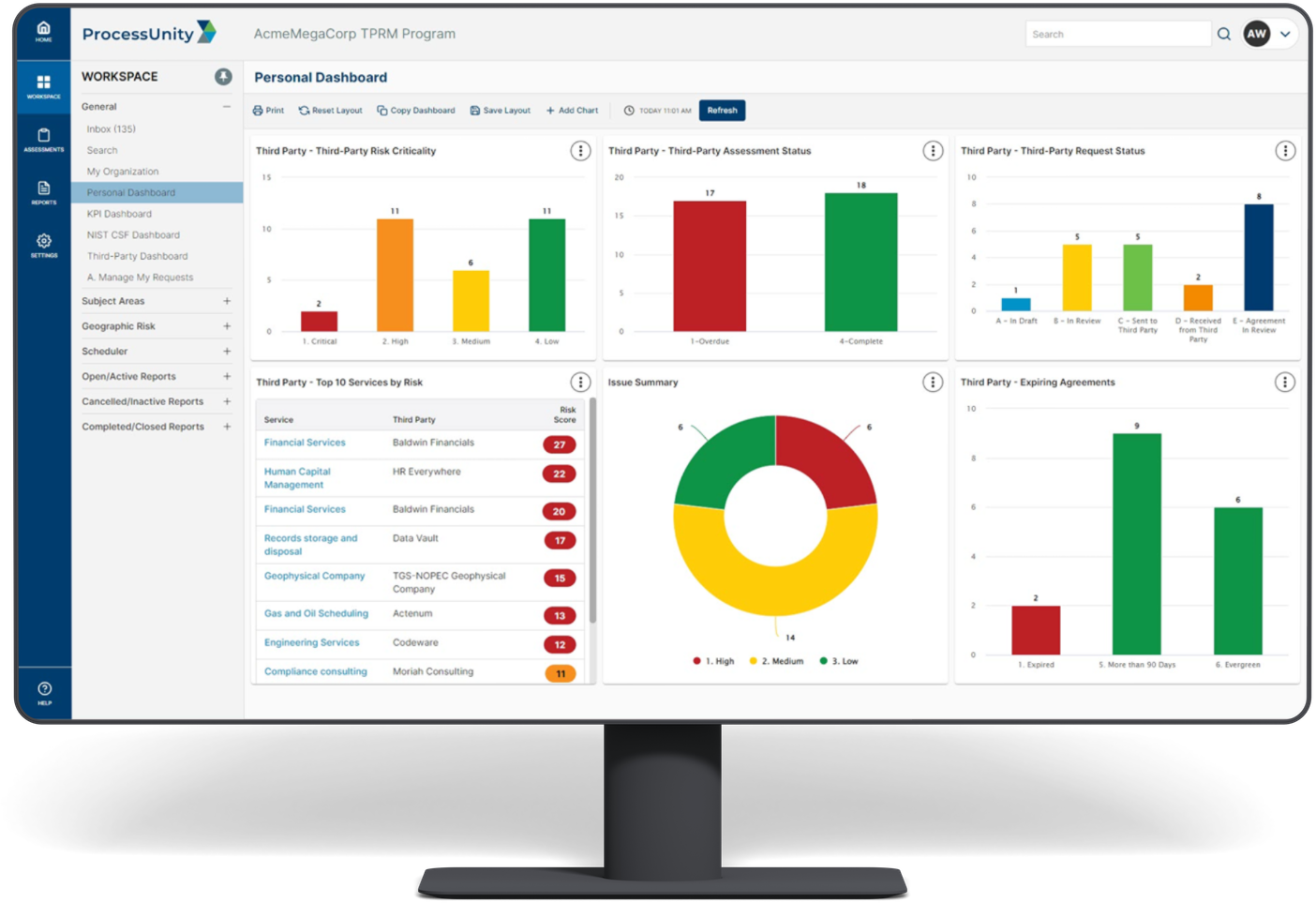
ProcessUnity offers pre-built integrations to BitSight Security Ratings to supplement your Third-Party Risk Program with objective cybersecurity ratings and rankings for an even more complete view of your vendor population. Whether during onboarding and initial due diligence or as part of your ongoing monitoring program, the ProcessUnity BitSight Connector integrates BitSight Security Ratings, Risk Vectors and questionnaire mappings into the ProcessUnity Vendor Risk Management platform to enhance visibility into cybersecurity risks and inform decision making throughout the entire vendor lifecycle.
Vendor Assessment ValidationValidate vendor assessment responses with unbiased cybersecurity ratings to ensure that vendors are within your organization’s cyber-risk tolerance levels. |
|
Continuous Vendor MonitoringTrack vendor cybersecurity performance over time and alert appropriate stakeholders in between periodic vendor assessments when cybersecurity ratings drop below specified thresholds. |
|
Effective AssuranceImprove cyber risk assurance for your entire vendor portfolio using cybersecurity ratings-driven workflows, collaboration and executive reporting |
BitSight On-Demand
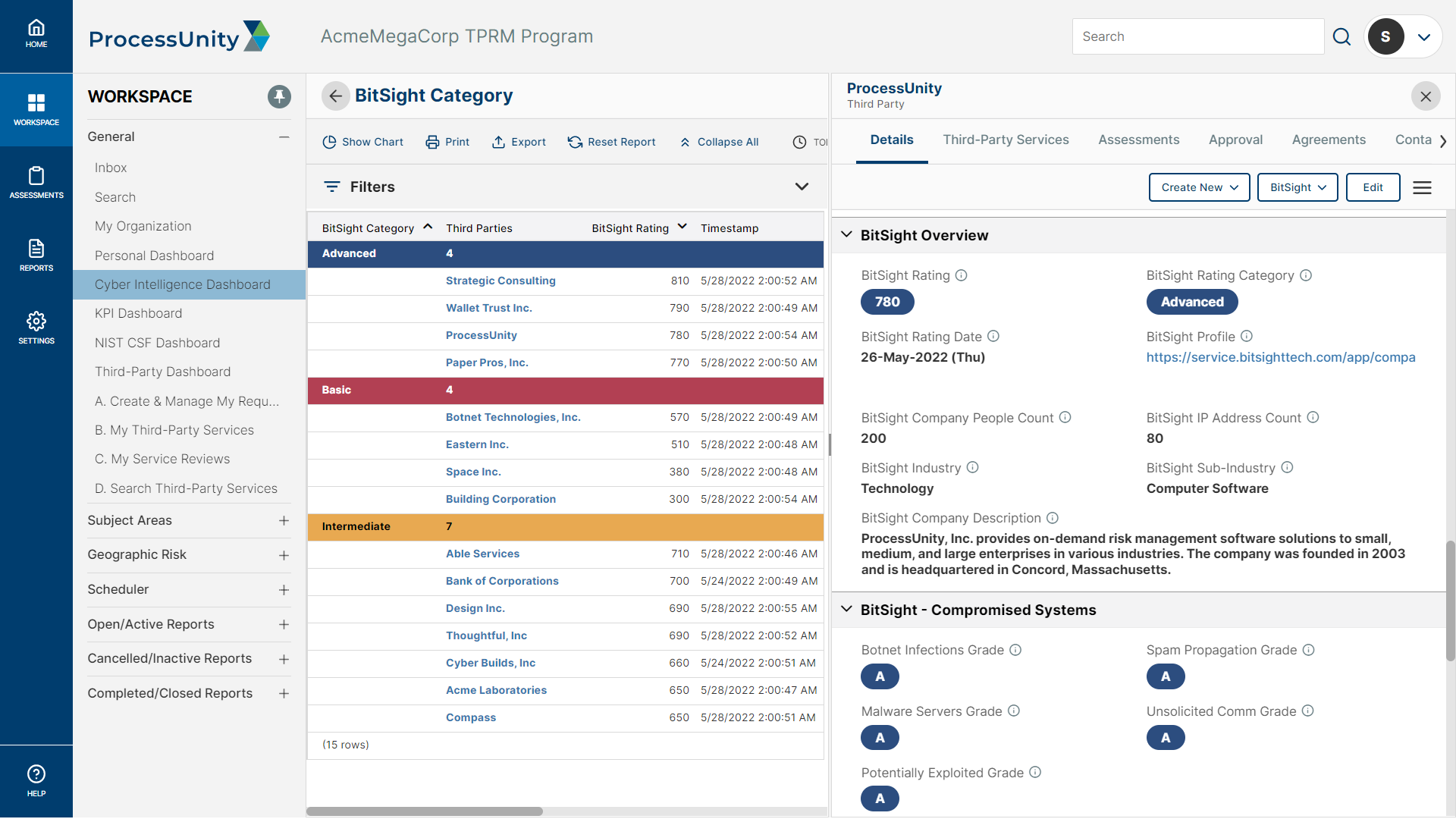
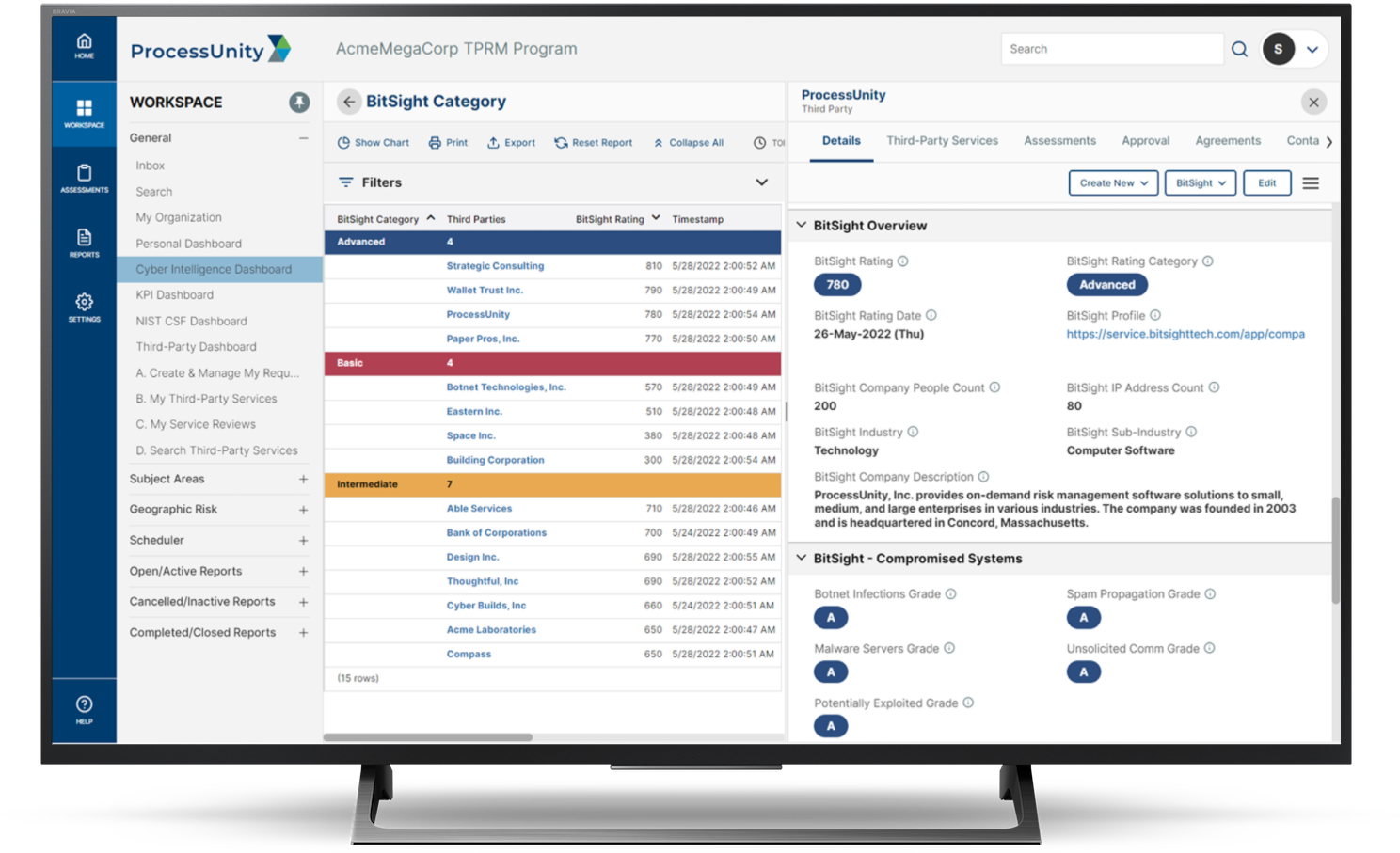
The ProcessUnity BitSight On-Demand integration provides visibility into vendor cybersecurity risk ratings and vectors to improve the efficiency and effectiveness of the onboarding, due diligence and assessment processes. Via a pre-built connector, BitSight Security Ratings and Rating Categories are updated daily while Risk Vectors and Questionnaire Mappings are pulled, on-demand into ProcessUnity Vendor Risk Management platform to improve risk quantification during vendor evaluations.
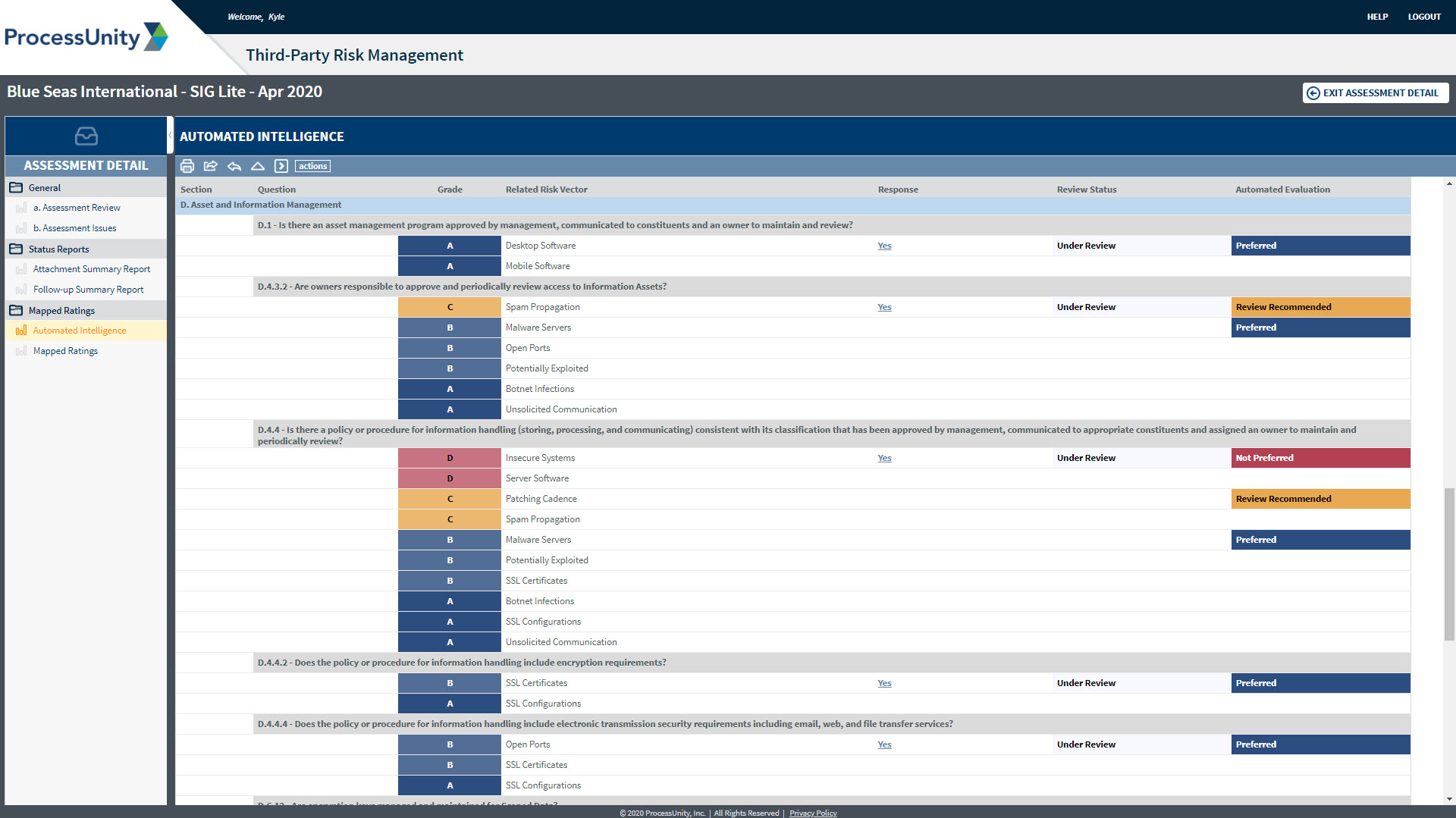
Third-party risk managers can leverage cybersecurity ratings and rating category data to add objectivity and context across their vendors and perform on-demand calls for updated risk vector and questionnaire mapping to lend additional insights during onboarding or periodic assessments. These ratings can also be used to inform inherent risk calculations for more targeted assessments and to correlate or validate the cybersecurity risk posed by each vendor. To streamline downstream workflows, BitSight rating changes or drops in scores below your organization’s designated risk threshold can automatically trigger notifications or issue creation to prompt further investigation.
Features & Benefits
-
Inform inherent risk calculations to auto scope vendor assessments
-
Validate vendor assessments responses using objective, evidence-based cybersecurity ratings
-
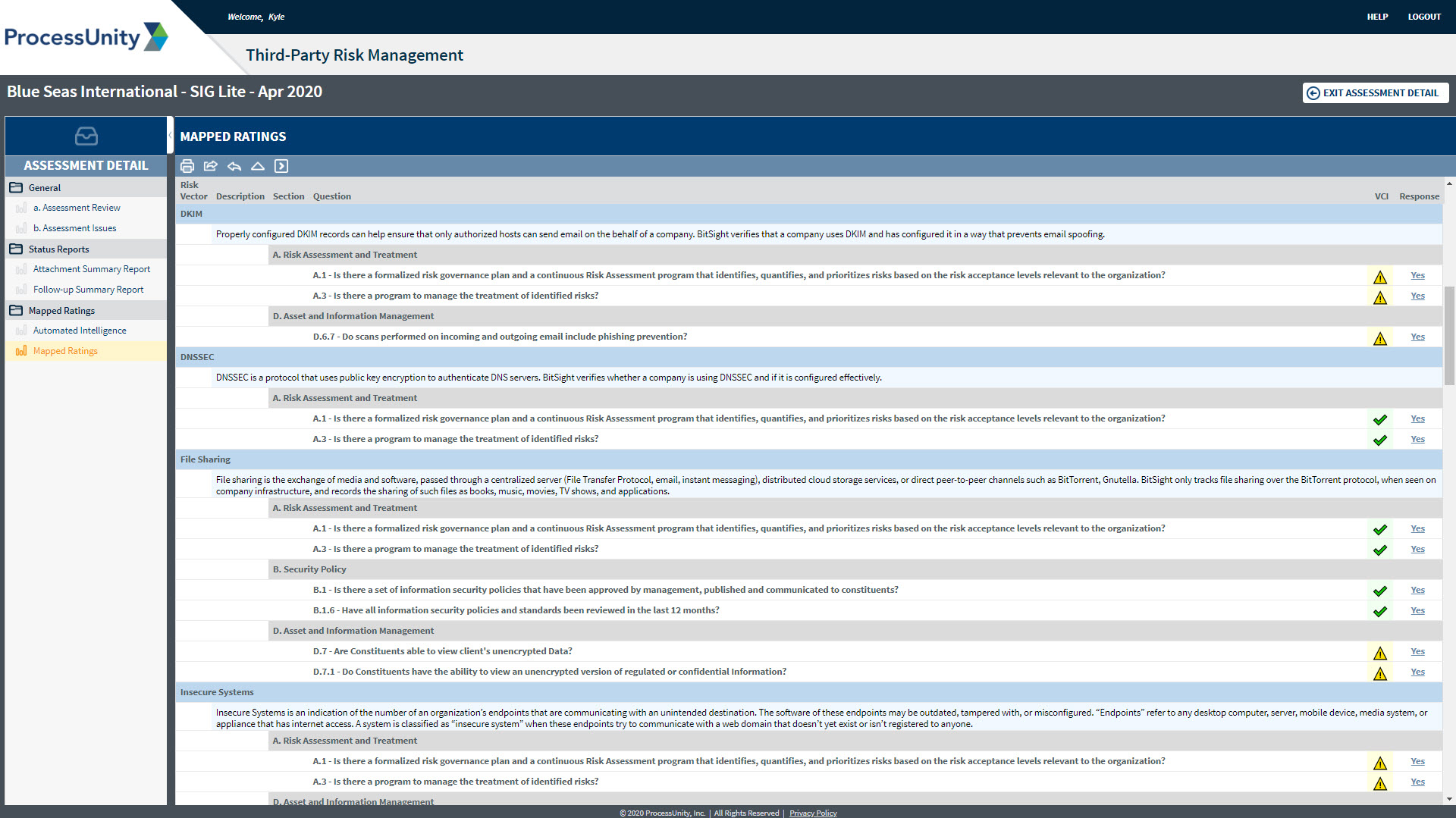
Attain complete cybersecurity coverage through risk vector to questionnaire mapping
-
Automatically initiate workflows, alerts and notifications based on changes to vendor cyber ratings
-
Access BitSight Risk Vectors and detailed descriptions from the ProcessUnity Vendor Risk Management platform
-
Leverage cybersecurity domain-specific dashboards and reports
BitSight Continuous Monitoring
ProcessUnity BitSight Continuous Monitoring integration delivers timely, data-driven insights into third party cybersecurity performance on your own predetermined schedule and includes access to BitSight’s Security Rating Platform for deeper analysis.
Ongoing refreshes of these BitSight security ratings, rating categories, risk vectors, and questionnaire mappings are visible directly within the ProcessUnity platform while a direct URL link allows users to easily access real-time BitSight vendor reports to view details behind each risk vector. Incorporating BitSight’s continuous security performance measurements into your assessment process facilitates more rigorous vendor due diligence, performance reviews and SLA monitoring.
The ProcessUnity BitSight Connector
ProcessUnity offers a pre-built connector that seamlessly integrates BitSight Security content into its Vendor Risk Management platform, using each vendor’s BitSight ID — eliminating the need to manually enter, recalculate risk scores, and/or continually update information on each organization being assessed. The ProcessUnity BitSight Connector provides visibility into the current security ratings of your vendors without having to move back and forth between a cybersecurity risk monitoring solution and third-party risk platform.
Additionally, the ratings and/or scores from BitSight can be incorporated into an overall risk calculation in ProcessUnity to determine assessment rigor or populate informative reports and dashboards for cybersecurity visibility and insights across your entire vendor population. The pre-built connector helps achieve integration easily which eliminates long waits for IT resource availability.
Request a Demo: ProcessUnity's Vendor Risk Management
Hundreds of organizations worldwide rely on ProcessUnity to make Vendor Risk Risk Management more effective and efficient. Schedule your personalized demo of our award-winning software and start your journey to a more mature, automated vendor risk management program today!
Request a Demo: ProcessUnity's Vendor Risk Management