Cybersecurity Performance Management
Cybersecurity Risk Administration
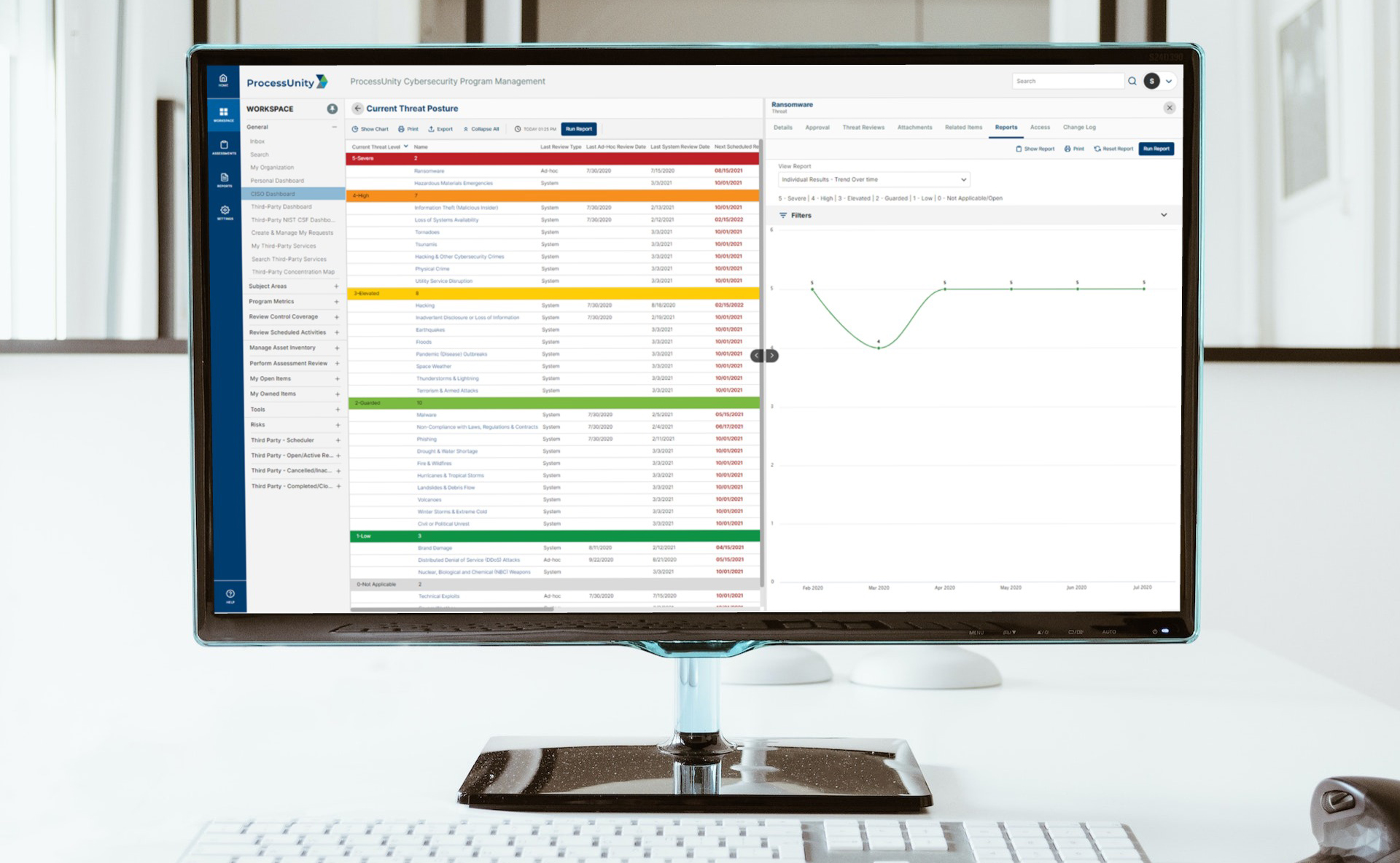
The Cybersecurity Risk Administration capabilities in ProcessUnity Cybersecurity Performance Management (CPM) trigger scheduled risk and threat reviews, capture responses and evidence, and automatically roll up metrics and trends into the ProcessUnity Cybersecurity Performance Command Center to guide risk mitigating activities.
Map Risks and Threats to Relevant Enterprise Controls, Industry Regulations and Standards
Rapidly evolving cybersecurity risks pose serious threats to your organization’s confidentiality, data privacy and operational resiliency. Modern cyberattacks such as ransomware and third-party breaches increasingly cause enormous business disruptions and financial losses across multiple industries. It is critical for your cybersecurity program to track, monitor, assess and prioritize all risks, threats and vulnerabilities that have the potential to adversely impact your organization’s operations, reputation or finances.
With ProcessUnity CPM’s Cybersecurity Risk Administration, organizations can:
- Identify, track and monitor risks and threats with the greatest potential for organizational impact
- Define risk categories, determine risk families and establish organizational risk groupings for remediation
- Map cybersecurity controls to risks and threats to increase control effectiveness
- Report on critical threats and risks organization-wide for visibility and project prioritization
Catalog and Track Risks and Threats
ProcessUnity Cyber Risk Administration provides a user-defined risk and threat register, categorized by criticality and aggregated into the appropriate internal groups. Based on your organization’s enterprise risk methodology, ProcessUnity CPM helps you to evaluate and maintain a list of risks and threats. These can be managed in alignment with the organization’s risk tolerance level for continuous control over risks that threaten your operations, reputation and finances.
Map Cybersecurity Controls, Standards and Regulations to Risks and Threats with the Cybersecurity Control Metaframework
ProcessUnity CPM provides a tailored control metaframework that eliminates control duplication across various regulations and standards such as NIST CSF, ISO 27002, GDPR and more. The platform maps a consolidated set of enterprise controls to risks and threats for deeper evaluation of control coverage, effectiveness and compliance. Furthermore, the metaframework improves visibility across your program, helping you to pinpoint risks as they arise.
Assess Risks and Threats via the ProcessUnity Control Evaluation Engine
Leveraging ProcessUnity Hands-Free Automation™, the ProcessUnity Controls Evaluation Engine sends risk and threat reviews to the internal owners responsible for oversight. The review results enable your cybersecurity team to prioritize and target risks and threats for remediation. Comprehensive mapping to your controls, standards and regulations allows you to identify where you need to adopt additional protective security controls.
Track Issues for Continuous Cyber Security Improvements
Real-time issue management with the ProcessUnity Issue Remediation Suite reduces the time it takes to create, track and remediate issues. Simultaneously, the platform systematizes the issue creation process to accelerate your remediation efforts. Leveraging a single location for managing these issues and their remediation plans, you gain complete control of all open projects tied to your control structure. Issues can be assigned severity ratings, and appropriate personnel can be notified to take any necessary action.
Leverage the Cybersecurity Performance Command Center for Real-Time Risk Intelligence
The ProcessUnity Cybersecurity Performance Command Center provides real-time visibility into the status of an organization’s risks and threats via drill-down capabilities, real-time tracking and historical analysis. Extensive, custom reporting capabilities allow you to create role-specific reports to help monitor, track and analyze your risks and threats. Tailored cybersecurity reports within the Cybersecurity Performance Command Center help demonstrate to executives and regulators the existence of a consistent, reliable process for managing risk. Reports also help cybersecurity teams identify critical control weaknesses across risk categories to provide insight into which controls need to be examined or improved.
Request a Demo: ProcessUnity's Cybersecurity Risk Management Platform
Hundreds of organizations worldwide rely on ProcessUnity Cybersecurity Risk Management to implement a centralized system of record for managing cybersecurity activities across the organization. Contact us to start your journey today!
Request a Demo: ProcessUnity's Cybersecurity Risk Management Platform